Let’s consider some ways to block access to the specific websites, domain names, URLs or IP addresses in Windows without using third-party tools. In our case, we will try to block certain websites using the built-in Windows 10 tools and PowerShell automation features.
Blocking Websites Using the Hosts File in Windows
The most popular method to block a specific website on Windows is to edit the hosts file. Usually it is located in %windir%\system32\drivers\etc\ directory. Please note that hosts file does not have an extension.
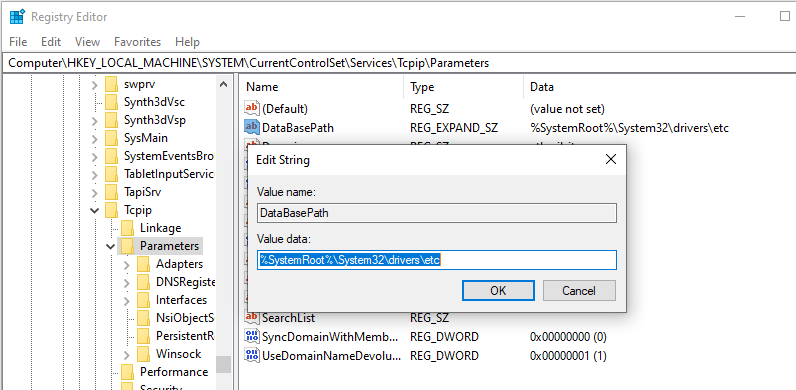
The hosts file is used to manually assign mappings between IP addresses and DNS names. When resolving names, the hosts has higher priority than DNS servers specified in the network connection settings.
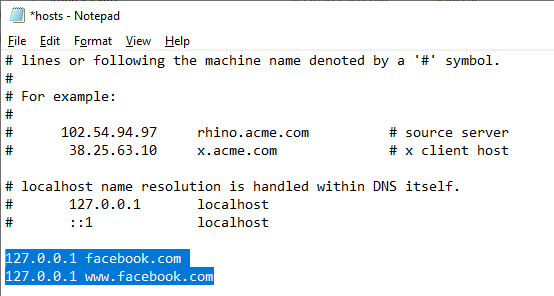
To block a specific website (for example, facebook.com), open the hosts file (with the administrator privileges) and add the strings like these to it:
127.0.0.1 facebook.com 127.0.0.1 www.facebook.com
Save the file and restart your computer (or clear the DNS cache using the command: ipconfig /flushdns).
After that, when trying to open the facebook.com in any browser you will see the message “Page not found” / “Page not available”.
You can add new lines containing website URLs to your hosts file using such a .bat file:
@echo off
set hostspath=%windir%\System32\drivers\etc\hosts
echo 127.0.0.1 www.facebook.com >> %hostspath%
echo 127.0.0.1 facebook.com >> %hostspath%
exit
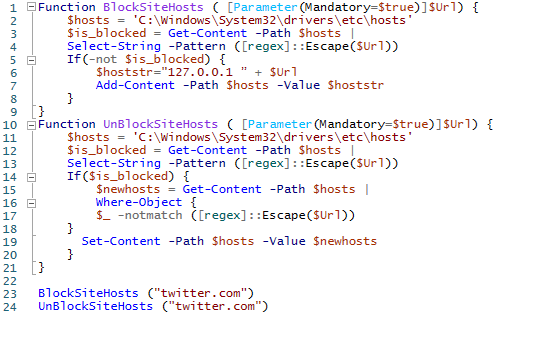
Or you can use the following PowerShell functions to automatically block specific websites in your hosts file.
Function BlockSiteHosts ( [Parameter(Mandatory=$true)]$Url) {
$hosts = 'C:\Windows\System32\drivers\etc\hosts'
$is_blocked = Get-Content -Path $hosts |
Select-String -Pattern ([regex]::Escape($Url))
If(-not $is_blocked) {
$hoststr="127.0.0.1 ” + $Url
Add-Content -Path $hosts -Value $hoststr
}
}
Function UnBlockSiteHosts ( [Parameter(Mandatory=$true)]$Url) {
$hosts = 'C:\Windows\System32\drivers\etc\hosts'
$is_blocked = Get-Content -Path $hosts |
Select-String -Pattern ([regex]::Escape($Url))
If($is_blocked) {
$newhosts = Get-Content -Path $hosts |
Where-Object {
$_ -notmatch ([regex]::Escape($Url))
}
Set-Content -Path $hosts -Value $newhosts
}
}
To add a website to the list of blocked URLs, just execute the command:
BlockSiteHosts ("twitter.com")
To unblock the website, run:
UnBlockSiteHosts ("twitter.com")
Block Websites Using DNS Filtering
If your clients use the same DNS server, in the same way you can block certain websites by creating a DNS entry in that DNS and specify something like 127.0.0.1 in it. By the way, most commercial DNS content filters (OpenDNS, SafeDNS, Cisco Umbrella, etc.) use the same principle.
How to Block Website IP Address in Windows Defender Firewall?
Also, you can block some websites using the built-in Windows Defender Firewall. The main disadvantage of this method is that you won’t be able to use the name of a domain or a website URL in the blocking rule. Windows Defender Firewall allows you to specify only an IP address or a subnet as a source/destination.
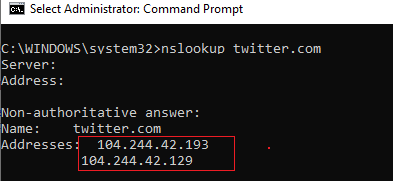
First of all, you have to get the IP address of the website you want to block. It is easier to do it using the nslookup command:
nslookup twitter.com
As you can see, the command has returned several IP addresses assigned to the website. You have to block all of them.
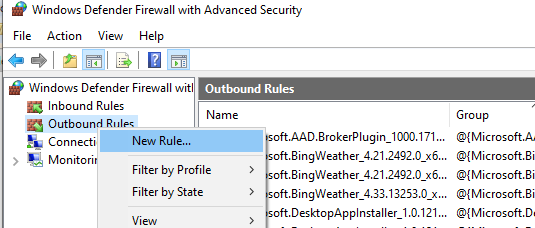
Run the Windows Defender Firewall management snap-in (Control Panel\All Control Panel Items\Windows Defender Firewall\Advanced Settings or by running firewall.cpl).
In the Outbound Rules section, create a new rule with the following settings:
- Rule Type: Custom
- Program: All programs
- Protocol Type: Any
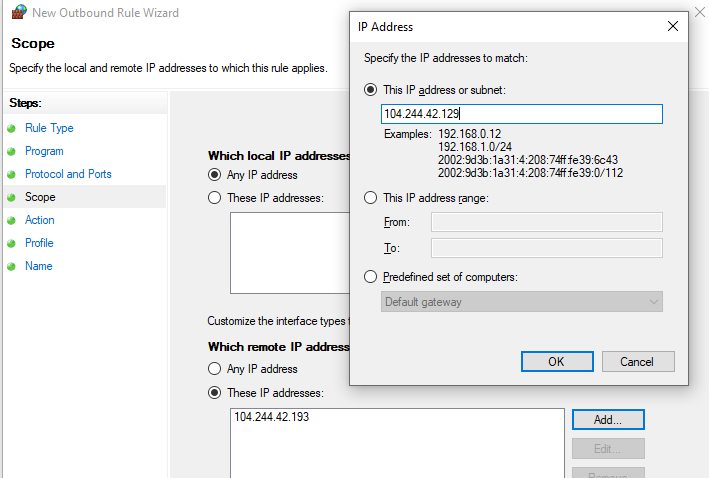
- Scope: In the “Which remote IP addresses does this rule apply to?” section select “These IP addresses” -> Add. In the next window, enter the IP addresses, subnets or a range of IP addresses you want to block.
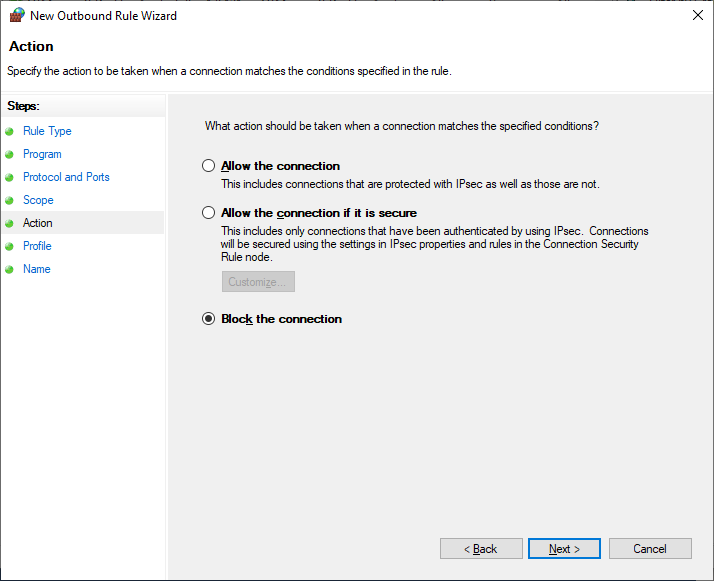
Click OK -> Next -> Action -> Block the connection.
Leave all options as they are in the window with Firewall profiles the rule is applied to. Then specify the rule name and save it.
After that Windows Defender Firewall will block all outgoing connections to the specified website’s IP addresses. The following message will appear in your browser when trying to connect to the blocked site:
Unable to connect
Or
Your Internet access is blocked Firewall or antivirus software may have blocked the connection ERR_NETWORK_ACCESS_DENIED
In your AD domain you can deploy a Windows Firewall policy to block access to a website on user computers using GPO. However, it is not rational. It is better to filter websites on your Internet access router (gateway).
Using PowerShell to Create Firewall Rule to Block Website by Domain Name or IP Address
You can also create a Firewall rule that blocks the connection to the website using PowerShell:
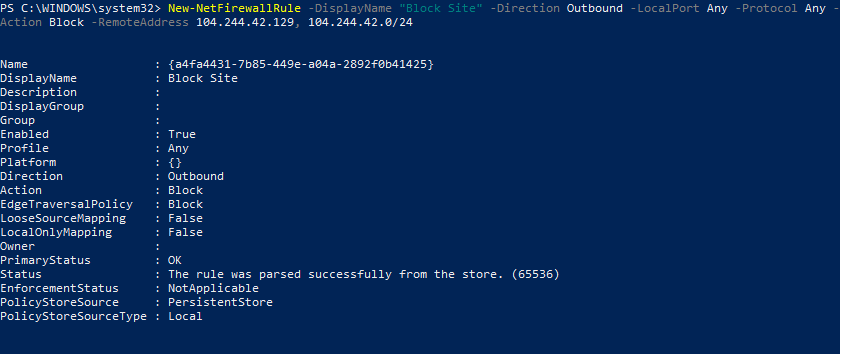
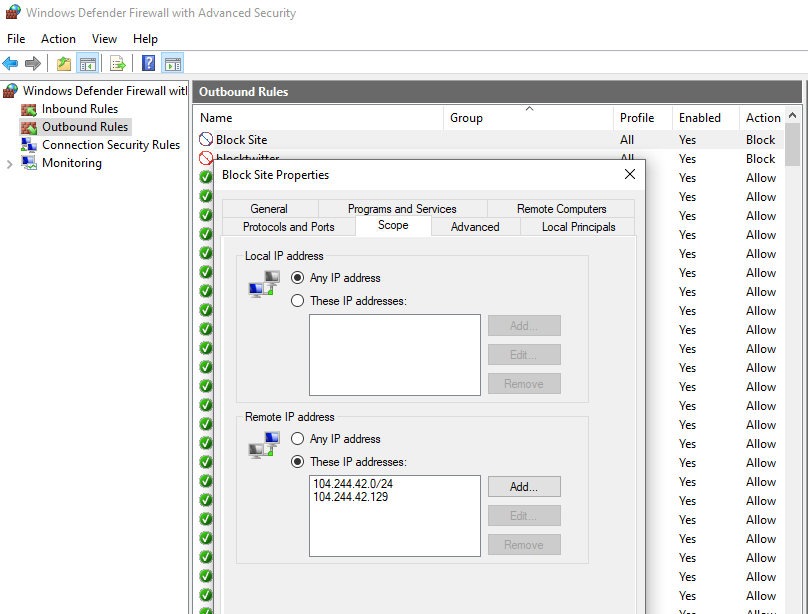
New-NetFirewallRule -DisplayName "Block Site" -Direction Outbound –LocalPort Any -Protocol Any -Action Block -RemoteAddress 104.244.42.129, 104.244.42.0/24
The string “The rule was parsed successfully from the store” means that the new Firewall rule has been successfully applied. You can find it in the graphical interface of your Windows Defender Firewall.
In order not to resolve the website names into IP addresses manually, you can use the Resolve-DnsName PowerShell cmdlet to get the website IP addresses:
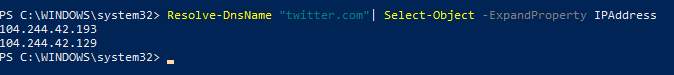
Resolve-DnsName "twitter.com"| Select-Object -ExpandProperty IPAddress
Thus, you can convert the name of the website into its IP addresses and add a block rule to the firewall settings:
$IPAddress = Resolve-DnsName "twitter.com"| Select-Object -ExpandProperty IPAddress
New-NetFirewallRule -DisplayName "Block Site" -Direction Outbound –LocalPort Any -Protocol Any -Action Block -RemoteAddress $IPAddress
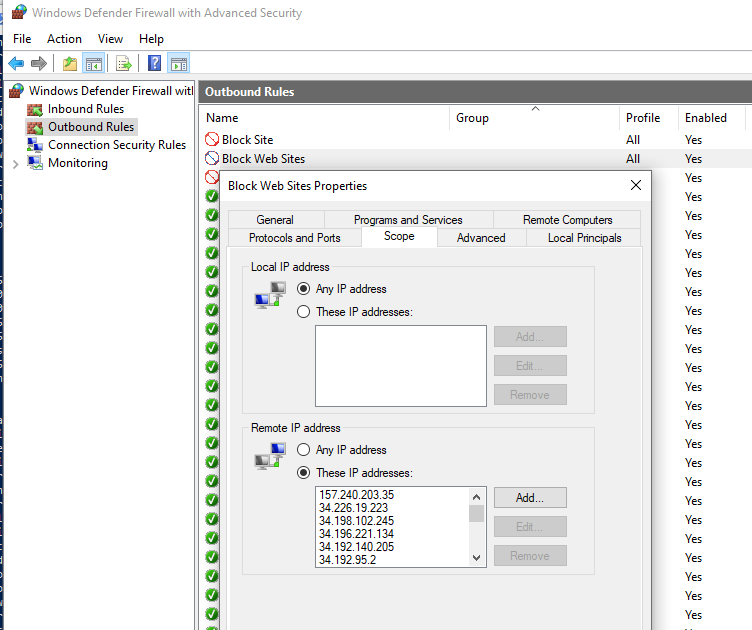
So you can now add a blocking rule to your Windows Firewall for multiple websites at once:
$SitesToBlock = "facebook.com","instagram.com","youtube.com"
$IPAddress = $SitesToBlock | Resolve-DnsName -NoHostsFile | Select-Object -ExpandProperty IPAddress
New-NetFirewallRule -DisplayName "Block Web Sites" -Direction Outbound –LocalPort Any -Protocol Any -Action Block -RemoteAddress $IPAddress
I have added the –NoHostsFile parameter to the Resolve-DnsName cmdlet in order not to use the hosts file for resolving.
Let’s make sure that a block outbound rule has appeared in the Windows Firewall console.
This article is mostly a brain training exercise. In a corporate network, you must use website filtering on your Internet access gateway, router or a proxy server. The host-level blocking is not very effective.
3 comments
Two points:
1. Resolving an URL to an IP and then blocking that IP is hardly a guarantee of prevention. In some cases, there are many IPs that lead to URL, in some cases an IP leads to many URLs which may be ones you need or want to get access to. You should mention this aspect when you talk about that aspect of things.
2. I just ran into the oddest scenario which has me now pointing undesirable URLs to an IP address in my local net that my DHCP server will never assign (nor will I) vs. the loopback interface (127.0.0.1). Why?
Well, I found with some of the google stuff I was trying to block and routed to 127.0.0.1, when I did a netstat -s or netstat -a -n -o, I observed that there were a bunch of connections targeted at the name the google software was looking for that had *CONNECTED* to something on 127.0.0.1 (both the local and foreign addresses were on the loopback interface). I bet there are apps that you want to block that act both as client and server so looping back forms a connection back to your own machine. While this does keep those attempts back within your machine, it still seems undesirable.
My solution here was to identify a network address locally that DNE and never will (outside my DHCP allocation pool, will not be statically created by me – which also implies that I have entire control over the network which I do) and then use the hosts file to send these requests to a dead end. Is that better than having them loopback, never hit the network, and connect to something locally? I really don’t know. I am hoping with the address translation from an URL to a host in the hosts file (to a dead address on the network) and then using Windows Defender to block outgoing requests for that dead IP, that combination will result in the firewall just quietly eating the outside connect requests so a) there will be no connections back to my machine in loopback and b) there will be no extra connection requests firing into the local network (because Defender blocked them).
Just some extra strategies for the thought experiment. I do appreciate the article for the knowledge you have conveyed – thank you.
One further point: If you don’t control the network, there are still ‘reserved’ internet address ranges that for the most part are not supposed to be used in normal networks. It is possible for you to use one of those ranges to send the requests to (as it isn’t likely to catch a host on your network) and then kill that address with IP based blocking in Defender Firewall.
Note, do not use the Link Address range (which is used for when a DHCP server is not available and DHCP clients are trying to assign themselves (no central direction) an IP address that does not conflict with another using trial-error-retry with new address approach). Leave that address band alone, but there are still other reserved address ranges you could use. I’d still put a Firewall block on outgoing traffic to those just to not put things onto your local net and make your router/switch/access point/etc have to make a decision about what to do with that traffic (why waste the devices time?). Block it locally as an outgoing address on your box.
In MOST cases, this approach should not impede any local software.
One somewhat useful (depends on how machines on your network setup ping handling) way to test a reserved address on your local net would be to ping it from the command line. That would tell you if it was occupied if you got a ping response. (Does not tell you nothing might be there if you do not – machine could be off temporarily or be set not to return ICMP echoes when pinged). But if you do get a response on a reserved internet address, try another. There are 3 or 4 ranges with a lot of addresses in them in the list of reserved addresses.
(PS I’m talking IPv4 here – haven’t looked into any reserved address ranges in IP V6)
Not sure how out of date this is, but the directory structure in REGEDIT is not the same. I am running windows 10.
I would suggest specifying the windows OS version in this, or just deleting it. Neither will happen probably. Just another Orphaned webpage on the vast superhighway of information.